• Long-form Position
• Practitioner-grade
Most AI sessions start the same way. The operator opens a conversation and begins re-explaining: what the project is, what happened last session, where things stand, what they’re trying to accomplish today. This re-explanation is invisible overhead. It costs time, it costs context tokens, and it costs the cognitive energy that should go toward actual work.
The cockpit session pattern eliminates this overhead entirely. The context is pre-staged before the session opens. The operator arrives to a working environment that is already mission-ready — client brief loaded, task queue clear, relevant history surfaced, tools oriented to the problem at hand. The warm-up is done before the session starts.
The name comes from aviation logic. A pilot doesn’t climb into the cockpit and begin configuring instruments. The pre-flight checklist runs before the seat is taken. By the time the pilot is in position, the environment is ready for work — not for setup. The cockpit session applies the same principle to knowledge work.
Why This Matters More Than It Looks
The cost of a cold session start isn’t just the five minutes of re-explanation. It’s the quality degradation that runs through the entire session while the AI is still assembling the picture. Early in a cold session, you’re managing the AI — filling gaps, correcting assumptions, orienting the system. Mid-session, you’re working with the AI. The cockpit pattern collapses that warm-up phase so the session starts at mid-session quality from the first message.
For a solo operator running multiple business lines, this compounds. If every client session starts cold, every session pays the loading cost. If four clients each require ten minutes of context reconstruction per session, that’s 40 minutes per week of re-explanation before any work begins — and the work done during re-explanation is lower quality than the work done after context is established.
There’s a second problem beyond time: decision drift. When every session reconstructs context from what you happen to mention that day, the AI’s understanding of your situation shifts based on what you emphasize. A context that was staged deliberately — including the things you’d otherwise forget to mention — produces more consistent output than a context assembled ad hoc from whatever is top of mind.
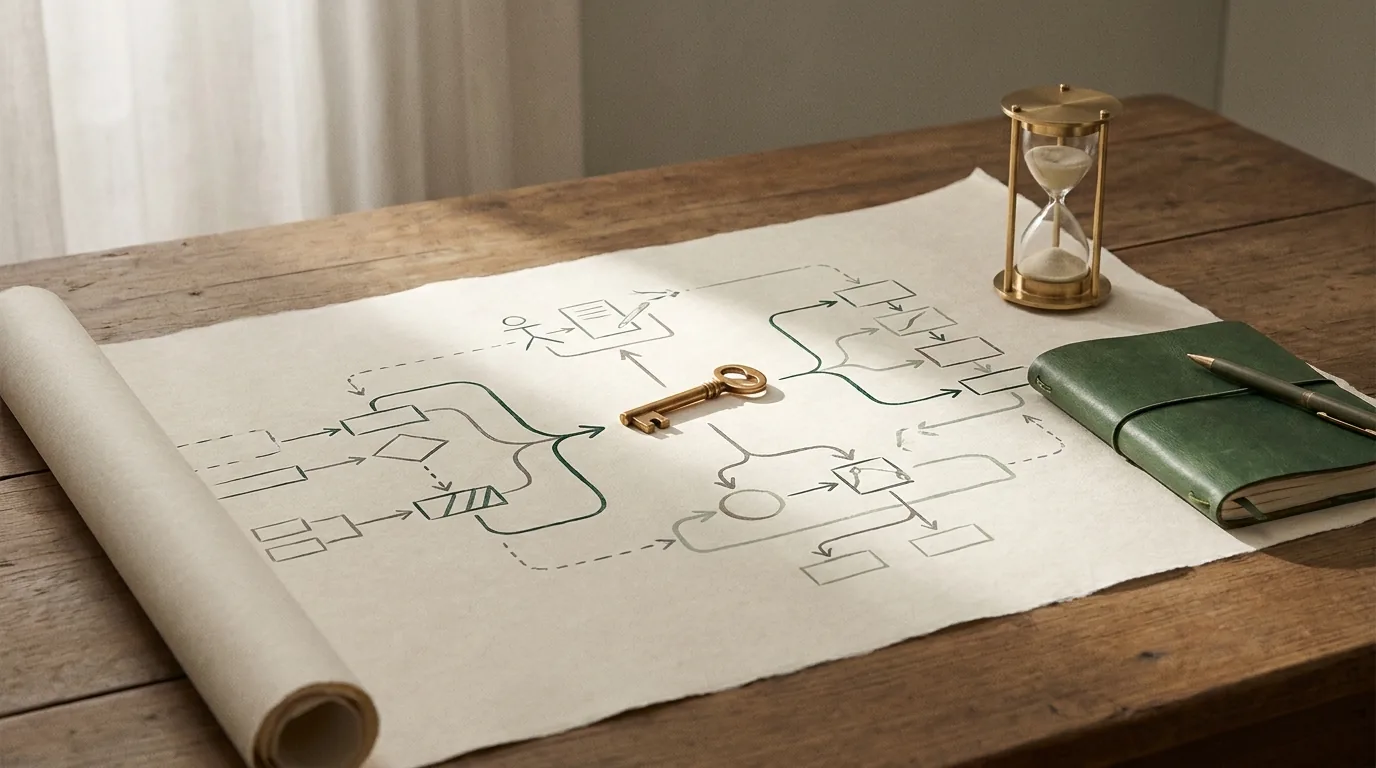
What a Cockpit Session Actually Contains
A properly staged cockpit has five components. The specifics vary by context — a client site session looks different from a content strategy session looks different from an infrastructure session — but the structure is consistent.
1. The active brief. What are we working on in this session specifically? Not a general description of the project — the specific problem or output for today. “Publish 12 articles to Partners Restoration and optimize for the custom home builder cluster” is a brief. “Work on Partners Restoration content” is not.
2. Current state. Where does the project stand right now? What was done in the last session? What is pending? This is the context that prevents re-work and prevents missing dependencies. In the Second Brain, this lives in the client’s Notion page — status fields, last session notes, pending task flags.
3. Hard constraints. What can’t we do, break, or change in this session? For WordPress work: the page guard rule, which sites use which connection methods, what was explicitly decided in prior sessions that shouldn’t be re-litigated. For content work: which keywords are already covered, which clusters are complete, what the taxonomy looks like. Constraints are the most expensive thing to discover mid-session, so they go in the cockpit.
4. Priority signal. If this session produces one thing of value, what is it? The single most important output. This prevents sessions that produce ten mediocre things instead of one excellent thing, which is the default failure mode of open-ended AI sessions.
5. Known failure modes. What has gone wrong in similar sessions before? The GCP/Vertex AI content rule — never write model specifications without live verification — is a known failure mode that belongs in every cockpit where GCP content might be produced. The page guard rule belongs in every WordPress session. Known failure modes in the cockpit prevent known failures in the session.
How the Cockpit Reduces Minimum Viable Executive Function
This is the piece that connects the cockpit session to the neurodiversity design framework it comes from. Executive function in ADHD is variable, not uniformly low. On a high-executive-function day, a complex multi-step session runs cleanly. On a low-executive-function day, the same session can feel impossible — not because the capability is absent, but because the activation energy required to start is higher than what’s available.
A cold session has high activation energy. You have to figure out where things stand, decide what to work on, load the relevant context into working memory, orient the AI to the problem, and then begin work. For a low-executive-function day, that sequence can be the entire obstacle.
A pre-staged cockpit has low activation energy. The state is already loaded. The priority is already identified. The constraints are already in the context. The question isn’t “where do I start” — it’s “do I proceed.” That’s a dramatically smaller decision to make, and it means that low-executive-function days can still be productive days rather than lost ones.
The infrastructure carries the initiation overhead so the operator’s variable executive function goes further. This is why the cockpit pattern is the single highest-leverage habit in an AI-native operation — not because it saves time, though it does, but because it extends the range of days when useful work can happen at all.
The Cockpit as Transferable Protocol
One of the underappreciated properties of the cockpit pattern is that it’s packageable. A cockpit that Will stages for himself runs at Will’s speed because Will knows what to put in it. A cockpit that’s been designed as a repeatable protocol — with a specific template, specific data pulls from the Second Brain, specific constraint checks — can be staged by anyone with access to the system.
This is the multi-operator scaling moment: when a second person (a developer, a contractor, a hired editor) needs to run a session that produces Will-level output, the cockpit protocol is the bridge. The institutional knowledge that makes Will’s sessions productive is encoded in the cockpit template. The new operator follows the protocol. The session starts at the same quality level.
Most operations don’t have this. The experienced operator’s sessions are good because of knowledge that lives in their head, not in the system. When they’re unavailable, session quality drops. The cockpit pattern makes session quality a property of the system, not a property of the individual — which is the design goal for any operation that needs to scale beyond one person.
Frequently Asked Questions
How long does it take to stage a cockpit?
For a session type you’ve run before: three to five minutes once the Notion pages and context sources are organized. For a new session type: fifteen to twenty minutes to design the template, then three to five minutes to run it going forward. The upfront design cost is paid once; the recurring benefit is captured every subsequent session.
What if the pre-staged context is wrong or outdated?
Correct it at the start of the session and update the source. The cockpit is the starting point, not the oracle. If the Notion page shows stale status, update the status before proceeding. The correction takes thirty seconds and improves the cockpit for next time. Wrong context in the cockpit is a data quality problem — fix it at the source rather than working around it each session.
Does this work without a Second Brain or Notion?
A simpler version works anywhere you can store context. A Google Doc with current project state, a notes file with known constraints, a short text file with today’s priority — these produce meaningful improvement over cold sessions even without a full Second Brain architecture. The full version with Notion, claude_delta metadata, and automated context pulls is more powerful, but the core behavior (pre-stage before you start) produces value immediately with whatever you have.
ADHD and AI-Native Operations Cluster
The ADHD Operator: Why Neurodiversity Is an Asymmetric Advantage (Pillar)
- External Working Memory Architecture: How the Second Brain Replaces What ADHD Can’t Hold
- Variable Executive Function as a Design Constraint
- Interest-Based Task Routing: Designing for ADHD Attention Architecture
Related: Build the System Around the Behavior, Not the Tool — the design philosophy this cluster applies.